Security researchers at this weeks Black Hat detailed a new type of DoS attach which targets layer 7 on the application stack (as opposed to layer 4, eating up available bandwidth with requests). [External Link]
Category: Crime
Rap News 6 – Wikileaks’ Cablegate: the truth is out there
Information Security News: Call for Papers: Cyber Security in International Relations
Information Security News: Call for Papers: Cyber Security in International Relations.
Forwarded from: Brent Kesler <bdkesler (at) nps.edu> Call for Papers: Cyber Security in International Relations Submissions due: February 1, 2011 Strategic Insights, an online journal published by the Center on Contemporary Conflict at the Naval Postgraduate School, is seeking scholarly papers on the role that cyber security and information and communications technology (ICT) play in international relations and the strategic thinking of state and nonstate actors. This issue of SI seeks to inform policy makers and military operators of lessons drawn from real-world experience with computer and IT issues. We seek assessment and analysis based on real-world events, not speculation regarding potential threats and perceived vulnerabilities. Papers that test or develop political theories and concepts are encouraged. We hold a broad definition of cyber security, and encourage submissions on a range of ICT topics related to threats to national security and individual liberties, responses to such threats from states and non-state actors, and emerging issues offering an over-the-horizon view of cyber security. However, all submissions should be empirically based; we do not intend to publish work purely devoted to editorial opinion, threat anticipation, or policy advocacy. Submissions therefore should attempt to map capabilities based on available sources or game out real-world implications based on empirical data; any "digital Pearl Harbor" scenarios should attempt to measure the extent of the damage--tangible, social, or political--that could occur. Sample Topics: * Use of cyber attacks to influence government behavior (e.g., 2007 Estonia attacks) * Cyber attacks as a force multiplier in conventional conflicts (e.g., 2008 Georgia attacks) * Internet as a critical resource for political and social movements (e.g., the Green Movement in Iran, electioneering in Moldova, Red Shirt Movement in Thailand) * Governments' efforts to contain popular movements that organize via IT (e.g., shutting down or containing flash mobs, Chinese monitoring of the Dalai Lama, software filtering and surveillance technologies) * The role of information technology strategies in the US and other states' foreign policy (e.g., US State Department intervention to prevent Twitter shut-down during protests following the 2009 Iranian elections) * Regional cyber-conflicts (e.g., North and South Korea, India and Pakistan, Israelis and Palestinians) * Espionage and secrecy in a networked world (e.g., China and Google, Wikileaks) * Information technologies, civil liberties and privacy (e.g., RIM Blackberry and Chinese, Indian and US efforts at surveillance; Wikileaks; the Safe Harbor dispute) * Strategic implications of cyber attacks against critical infrastructures * Innovative cyber attacks (e.g., Stuxnet and the Iranian nuclear program) * International cooperation to manage cyber-security and IT issues (e.g., Internet governance, WSIS, ICANN, WIPO) Submission Details: Submissions should be addressed to SI Editor Brent Kesler and sent in MS Word compatible format to ccc (at) nps.edu. They should range from 10 to 20 pages, double spaced, or 3,000 to 6,000 words. For more information on submission guidelines, please consult: http://www.nps.edu/Academics/Centers/CCC/Research-Publications/StrategicInsights/submissions.html
Time to put on the big thinking hat!
Digital Forensics Comes to VT Police
7 Days Newspaper publish an cover story article last week about the developing digital forensics culture in Vermont. [LINK HERE]
When Lawyers & Financiers attack
Ellis says the city is hoping it won’t have to pull fiber optic cable out of the ground to return the property to leaseholder CitiCapital. Instead, the city hopes to be able to find the same kind of cable and that it can then turn over to CitiCapital.
via Vermont state board hears from Burlington Telecom | The Burlington Free Press | Burlington, Vermont.
Pull fiber from the ground to recoup debt? WTF? Last time I checked recovered fiber wasn’t worth anything. And most of the money spent was in installation. And it cost a ton to remove it in the first place.
And if you can find the “same kind” of cable, why don’t you just give them cash? Or does BT has a secret stockpile of cable.
I’ve always figured that CitiCapital would be pulling equipment from the core. Say some routers & switches? Or something from the IPTV head end. At least there is a resale market for that stuff.
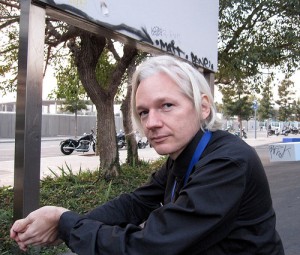
‘Operation Payback’ declares cyber war in Defense of Assange
A group of hacktivists attacked PostFinance in Julian Assanges name, calling for retribution and justice. [LINK HERE]
More on Assange Criminal Case
A sharp critique about the “political” motivations of the Assange case.
The fact is, we just don’t know anything right now. Assange may be a rapist, or he may not. His accuser may be a spy or a liar or the heir to Valerie Solanas, or she might be a sexual assault victim who now also gets to enjoy having her name dragged through the mud, or all of the above. The charges against Assange may be retaliation for Cablegate or (cough) they may not.
Public evidence, as The Times noted, is scarce. So, it’s heartening to see that in the absence of same, my fellow liberal bloggers are so eager to abandon any pretense of healthy skepticism and rush to discredit an alleged rape victim based on some tabloid articles and a feverish post by someone who is perhaps not the most trustworthy source. Well done, friends! What a fantastic show of research, critical thinking and, as always, respect for women.
Whatever the Julian Assange arrest is about, it’s not about how much women suck – Boing Boing.
Remember boys and girls, if your going to play super spy games keep it in your pants.
THOSE BASTARDS ARRESTED JULIAN ASSANGE
Julian Assange was arrested today in Britain and held on (false?!) allegations of rape and molestation. This is obviously a politically motivated arrest and a bunch of bullshit if you do the research. [LA Times Article]
Chuck Norris botnet karate-chops routers hard
The Chuck Norris botnet has been exploiting the hell out of unprotected routers still using default settings. CHANGE YOUR DEFAULT PASSWORD!
Damballa 2011 Threat Predictions
It’s that time of year for predictions of what will be coming our way in 2011. In many cases the security predictions you’ll read have a certain flamboyant air to them as they drop a clangor or two about how the world will be a better or more miserable place – from past experience those clangors are either completely off piste, or are an obscure spin on some well studied trend that’s been underway for a couple of years already.
So, with that cynicism behind us, instead of a bunch of “predictions”, I’m going to offer up a nice round number of 10 threat “expectations” for 2011:
Gunter what I’m hearing is that I’m going to need more of your services